Four loops. One binary.
SafeHarbor observes every asset, scores every vulnerability, drafts every SSP, and executes every remediation. Built as a single binary so it runs the same way on your laptop, on a hardened enclave appliance, and on a cATO-authorized SIPR node.
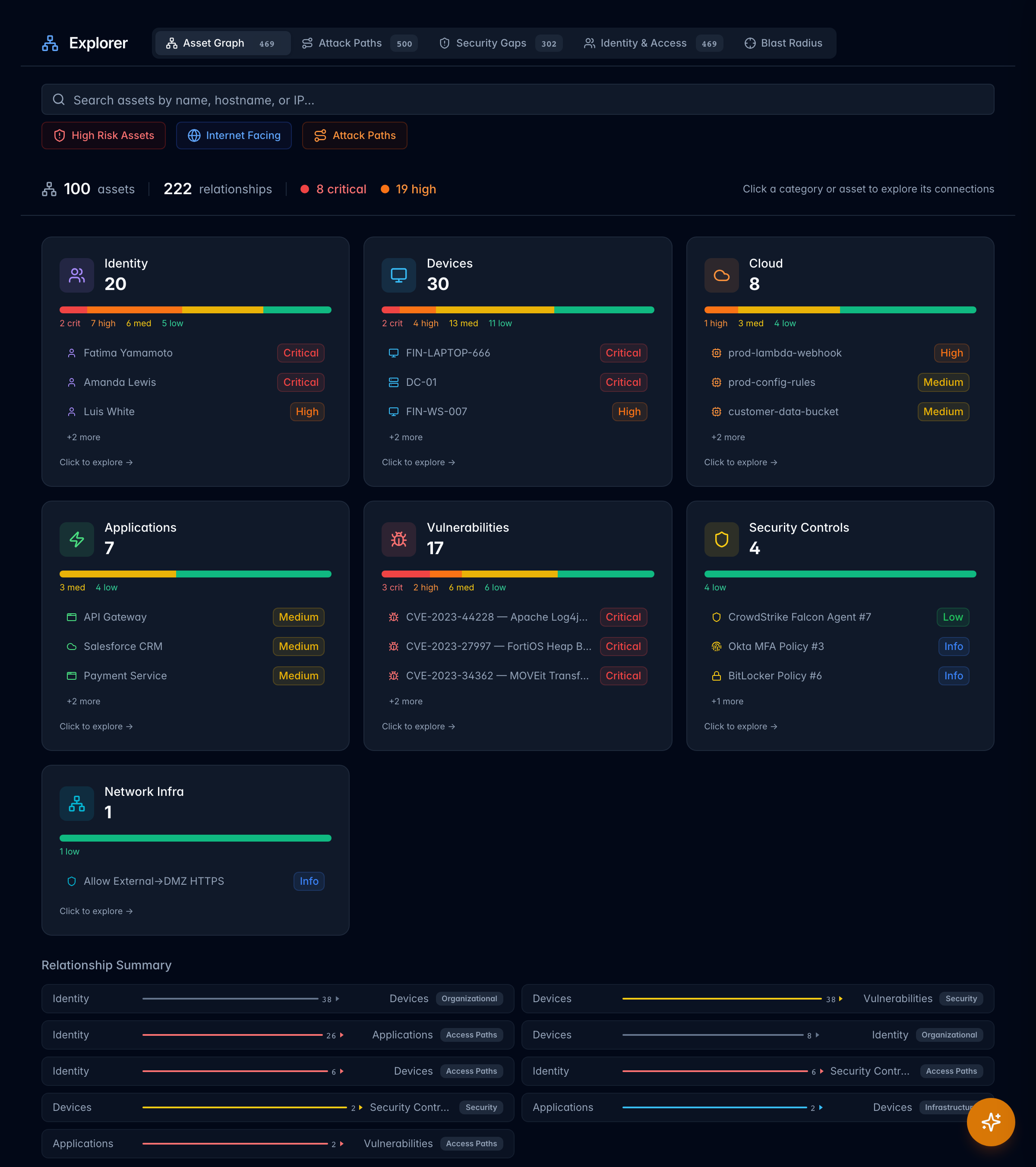
Every asset.
Every edge.
Every time.
1,264 connectors stream into a DGraph-backed asset graph with 23 AD edge types. ClickHouse handles the analytics side-car. NATS JetStream keeps the ingest pipeline durable even across air-gap transfer windows.
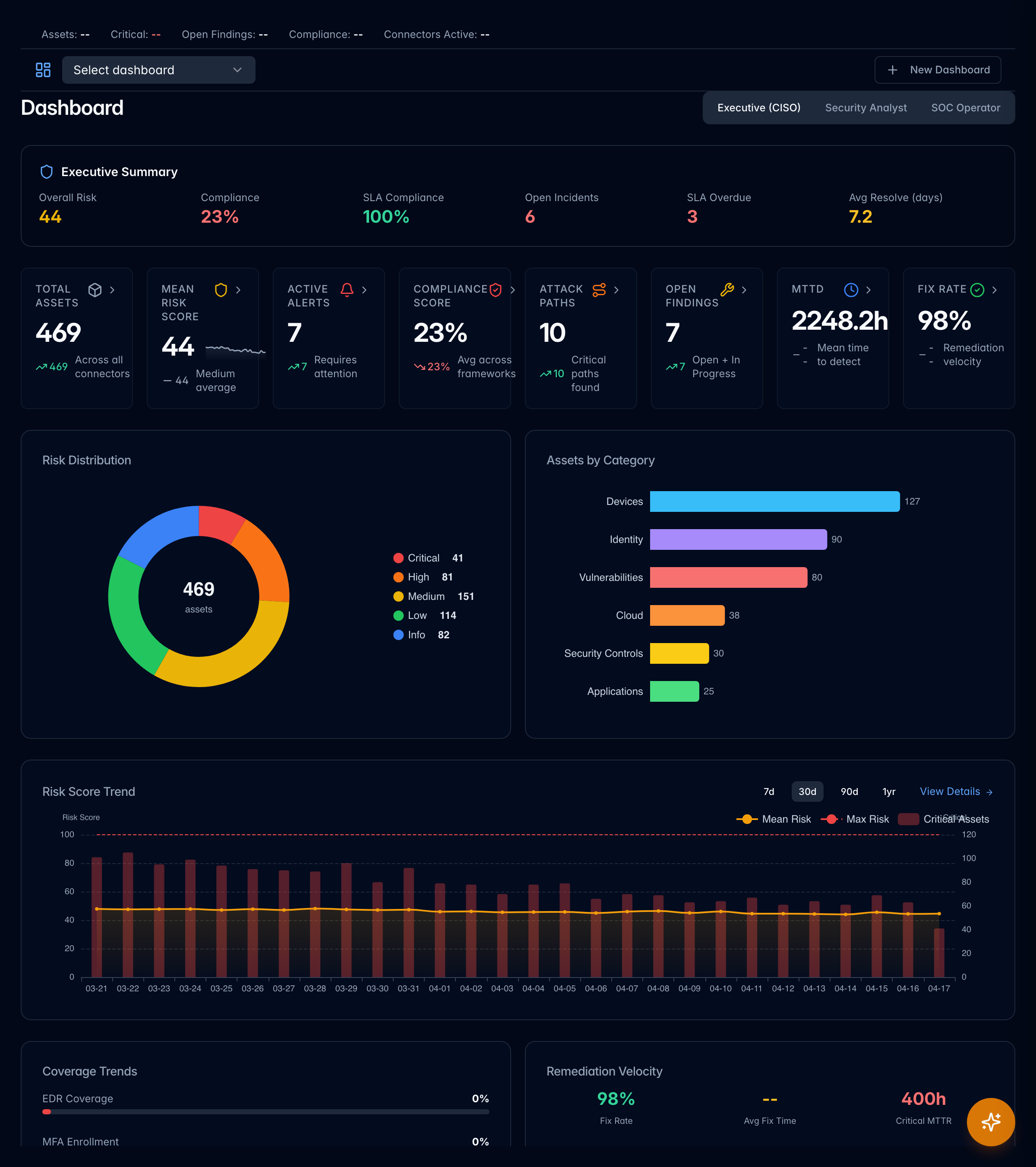
TIDE risk scoring. Predictive, not reactive.
Every asset carries a TIDE score: Threat, Impact, Defensibility, Exposure. Enriched with EPSS, CISA KEV, and Tenable VPR. Snapshots persist to ClickHouse, so you can query what the tide looked like at 4am last Thursday.
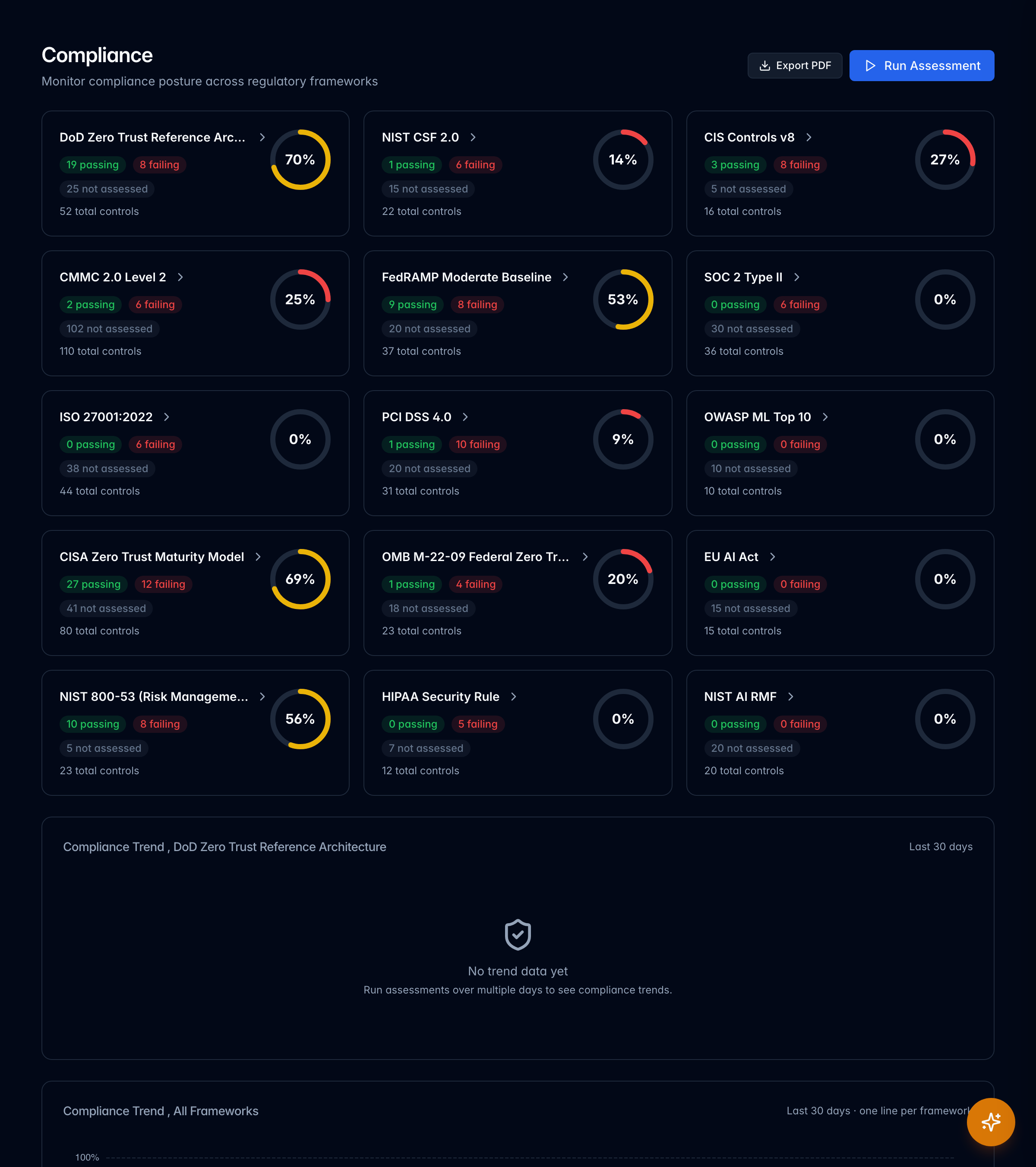
OSCAL-native compliance. Eight frameworks out of the box.
NIST 800-53 Rev 5, FedRAMP, CMMC 2.0, CISA BOD, CISA ZT, DISA STIG, PCI DSS, HIPAA. Auto-generated SSPs, evidence collection, and OSCAL export (SSP, SAR, POA&M, Component Definition). eMASS and Xacta 360 integrations ship in the box.
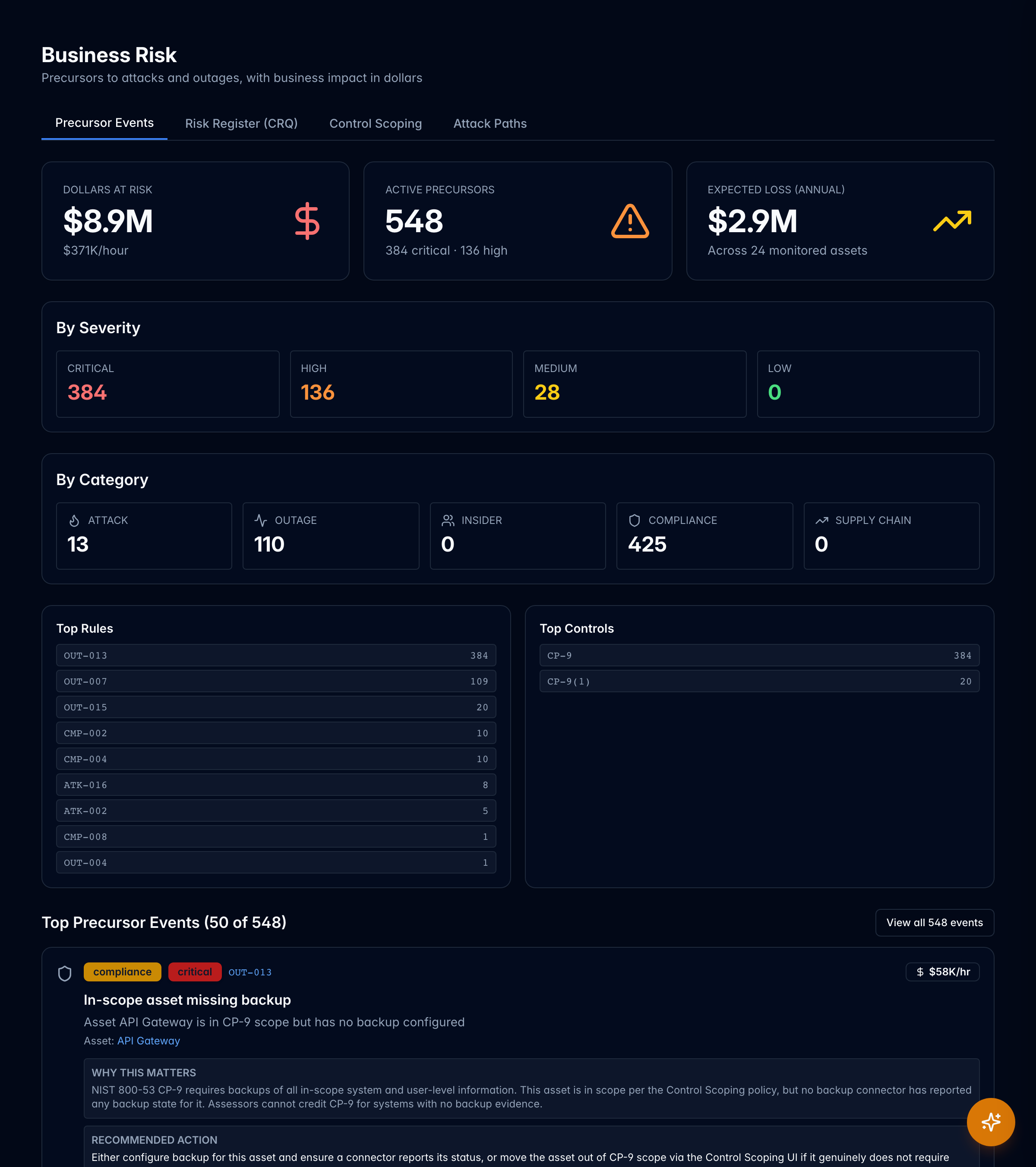
Closed-loop remediation. Not a ticket queue.
Policies declare desired state. SafeHarbor detects drift, opens change records, executes remediations through the same connectors it reads from, then proves the fix held. Every action signed and logged to the tenant-isolated audit stream.